Vikas on the Microsoft Office Trustworthy Computing security team explains how a new feature in Microsoft Word 2010 called Protected View.
In his article he discusses how hackers have discovered ways to manipulate Office binary files so that when they are opened and parsed, they cause their own code embedded within the file to run. To address these binary file parsing attacks in Office 2007, several new XML based file formats were introduced.
 One of the new features in Microsoft Word 2010 is the Protected View, which lets you open a Word/Excel file over the web — via Microsoft’s intermediate sandbox — and then display it for you if it’s deemed to be safe to open.
One of the new features in Microsoft Word 2010 is the Protected View, which lets you open a Word/Excel file over the web — via Microsoft’s intermediate sandbox — and then display it for you if it’s deemed to be safe to open.
What is Protected View?
Protected View is a new security defense-in-depth features added in Office 2010.
- In Office 2010 when a file appears to be from a potentially risky location, such as the Internet, it is opened in Protected View.
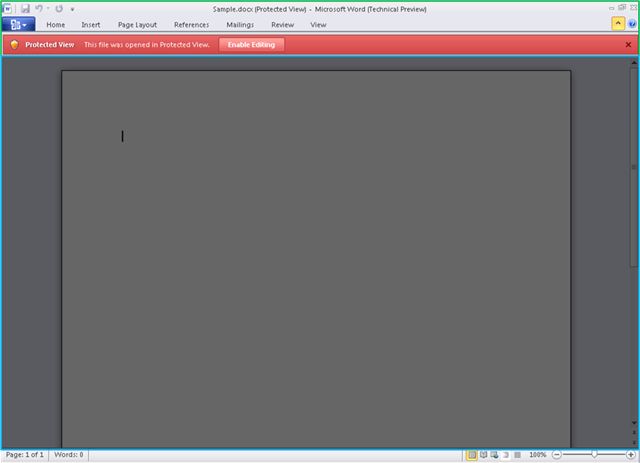
- Protected View appears like any other read-only view.
- When the file is opened in Protected View, it is being opened in the new Office 2010 sandbox.
- Office 2010 sandbox is the “next version” of the MOICE sandbox, thought no file conversation takes place.
- What happens is that the file is opend within a sandboxed instance of the application (e.g. Word, Excel, PowerPoint) and if there was malicious code present in the file, the code will not be able to tamper with your documents; change your profile or other user settings.
When is Protected View used?
Microsoft’s goal when designing this feature was to only use it in high risk scenarios:
1. Files opened from the Internet.
When a file is downloaded from the web, the Windows Attachment Execution Service places a marker in the file’s alternate data stream to indicate it came from the Internet zone.
When a Word, Excel or PowerPoint file is opened — and has this marker — it opens in Protected View until the user decides to trust and edit it. To do this, press Enable Editing.
Attachments opened from Outlook 2010
When an attachment is opened from Outlook 2010 it opens in Protected View. Administrators can configure if they want all attachments to open in Protected View or just those sent from senders outside their Exchange environment.
Files opened from unsafe locations
For example, files opened from your Temporary Internet Files folder. You can extend this list to include directories you feel are also unsafe.
Files blocked by File Block Policy.
Microsoft introduced File Block in Office 2007 which lets administrators define file types that should not be opened.
In Office 2010 these blocked files can now be opened in Protected View and you can set policy to indicate if the user should be allowed to leave Protected View (by editing the file) or force them to stay in it.
Office File Validation failures
This scans an Office file when it is being opened and validates it against a well-known schema. When there are inconsistencies between the file and the schema, the file will fail validation and opens in Protected View.
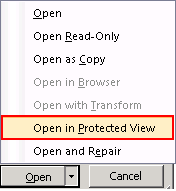
File Open Dialog
You can open files in Protected View explicitly by using the Open button.
As Vikas discussed, Protected View is one of the new security defenses in Office 2010.
For a malware to be able to run in Protected View, it will need to find a way around DEP, ASLR, GS and the 2010 Office File validation checks. And after all that, the malware would need to find a way to break out of the sandbox.
For sure, this is a step in the right direction from Microsoft. The next time you received a ‘scary’ Word file, you can open it in Protected View and read it without having to worry that something bad could happen to your computer.